Solutions
BYOD Solutions
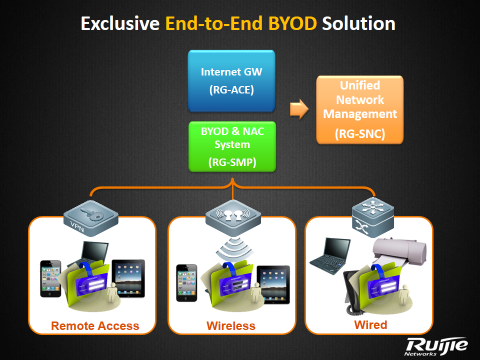
Ruijie offers a comprehensive solution to address an extensive array of BYOD requirements and challenges such as wireless coverage, access control and unified management. The architecture design of the solution is as follows:
-
Wireless coverage
- X-Sense and i-Share wireless coverage solution
- 802.11n and 802.11ac Gigabit WiFi
- Simultaneously manage at least 100 wireless access points (APs)
-
Access control
- Seamless staff wireless authentication
- Role-based network access control
- Self-service Email/SMS guest account management
- Unique QR-Code guest authentication
-
Unified management
- Visualization management of wireless device and remote fault location
- Unified management of wired, wireless and Virtual Private Network (VPN) users
- Integration with Identity Management System (e.g. LDAP, Microsoft AD)
- Proactive alert management via Email / SMS
Features:
-
Share Technology
For the deployment of BYOD, full wireless signal coverage is a basic requirement because users need to access the internet anywhere at the workplace using mobile devices. Therefore, the wireless signal must be able to cover every corner so as to support the BYOD deployment.
-
X-sense Smart Antenna
The strength of antenna plays an even more important role in BYOD deployment. Commonly used mobile devices are generally weaker in wireless reception performance than traditional laptops. WiFi signal has to be strong enough to cover such devices.
-
Seamless Authentication Technology
Seamless Authentication Technology specifically refers to the automatic authentication of end users to access the wireless network securely without the tedious process of entering account password and verification.
-
Guest account management technology using QR code
Guest account management technology using QR code refers to the authentication of guest account by authorized staff without the need of setting up an account and other management operations by the network administrator. Through binding of the guest and staff accounts, the browsing history of the guests can be retained for future reference.

